Individual forensic Bitcoin analyzes
Because every case is special
All of these scenarios require a different analyze
For this purpose, we create analyze-methods that are precisely tailored to your case.
This applies to the analyze-algorithms used as well as to the additional investigations such as analyzes of tax data, owner investigations, search for clues on the Internet, etc.
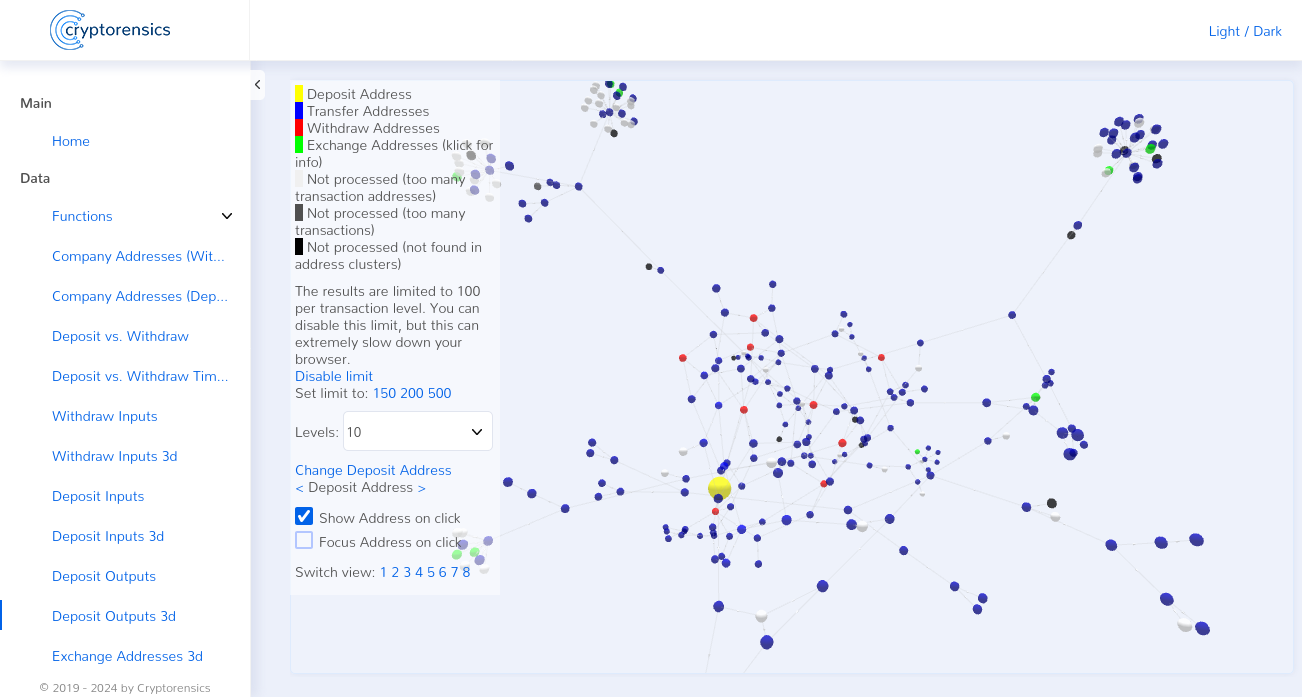
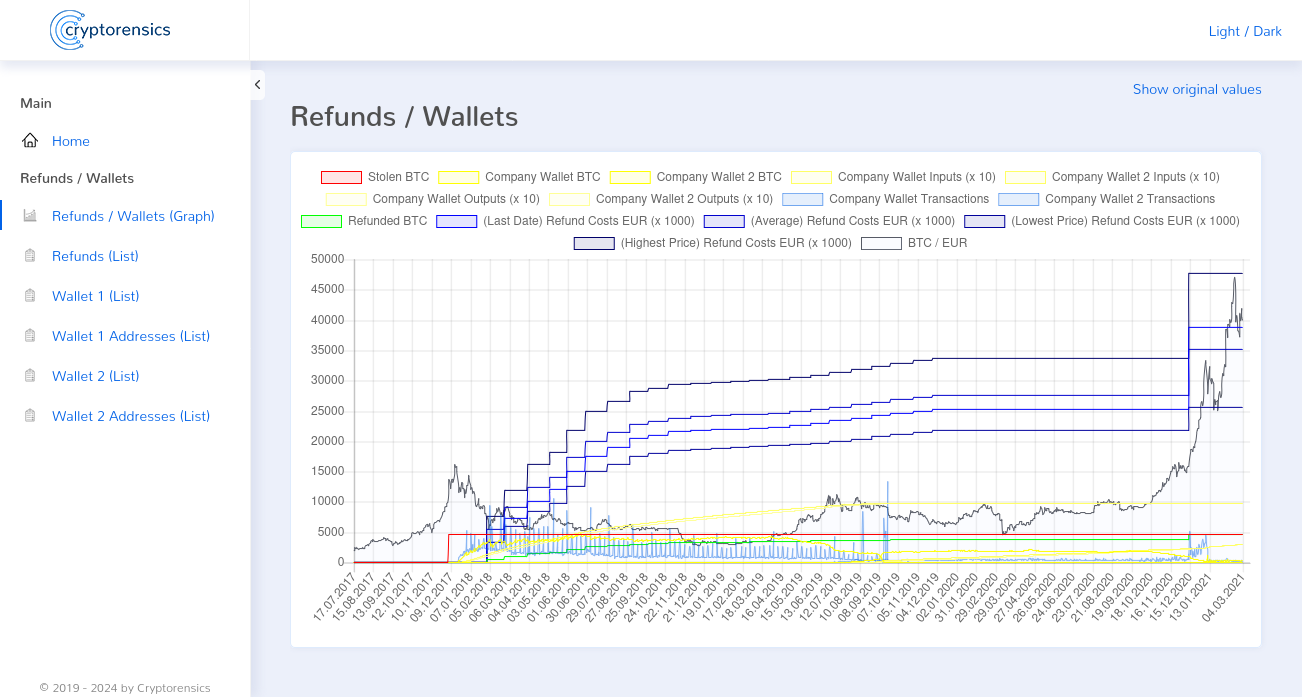
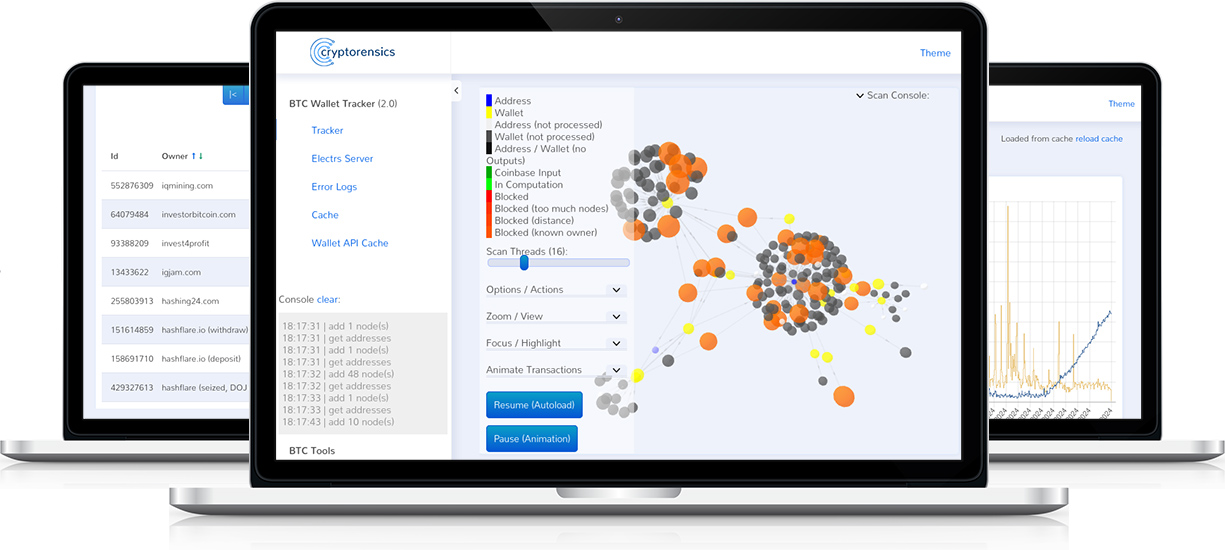
Our Tools for your success
We rely on software developed in-house for our analysis.
This enables us to clarify even the most complex cases – including yours.
Our core competencies
Find out more about the aspects of our work to which we attach particular importance.
Our Cooperations
In most cases, we work in close cooperation with the following customers and clients.
Authorities & Institutions
Cryptocurrency companys
Since we specialize in representing the victims of the crypto industry, we will, out of deepest conviction, not work for this industry. Learn more about this.
With you
If you are interested in a cooperation with Cryptorensics, we look forward to hearing from you.
If you have been the victim of crypto fraud, you can report your case to us here. The report scam function is of course completely free of charge for you!
If you would like to commission us with a case analysis, we recommend that you first visit the How we work page. There is a charge for these analyses (only if successful).
A selection of our previous projects
To give you an idea of our work, here is a small selection of our previous analyses.